The Client
Cachet is a financial services marketplace for gig workers; they aggregate and enrich cross-market data from gig platforms to enable businesses like insurance companies to sell better-priced and personalized coverage based on workers’ actual work hours. In 2022 investors supported their goal to build and scale tailor-made insurance products and services for platform workers by backing them with €5.5m in investment.
- Industry:Insurance
- Company Size:11-50 employees
- Country:Estonia
Challenges
Cachet’s engineering team was operating a production environment they couldn’t fully see or trust. Two compounding problems were undermining their ability to serve customers:
- Lack of visibility — the production environment had no reliable observability layer, making it difficult to identify problems before they became customer-facing incidents.
- Unreliable monitoring — operators had no trustworthy signal to confirm that the platform was performing as designed, leading to reactive rather than proactive incident response.
In the gig economy, platform workers depend on Cachet’s systems to file claims and receive timely responses. Downtime is not an inconvenience – it is a direct financial impact on customers. The lack of a structured DevOps practice meant that application development and infrastructure were managed in silos, compounding the reliability risk as the platform scaled.
Solutions
Cloudvisor proposed a phased approach: first, rebuild the infrastructure foundation using modern DevOps practices; then transition Cachet onto a Cloudvisor Managed Service (CMS) subscription for continuous operational ownership.
Infrastructure transformation
- Terraform IaC — Full Infrastructure-as-Code rollout across all environments, replacing ad-hoc manual deployments.
- CI/CD pipelines — Automated deployments through Bitbucket Pipelines triggered by version tags, with environment-dependent variable injection.
- Amazon EKS — Production workloads moved onto managed Kubernetes with a modular deployment flow (network, frontend, compute, database, services, observability).
- Observability — Amazon OpenSearch replaced the legacy ELK stack, with tailor-made monitoring and alerting delivering immediate reliability improvements.
- Identity & storage — Centralised IAM with environment-scoped roles; Amazon ECR for container images; KMS for encryption at rest.
The architecture of a Production account on AWS:
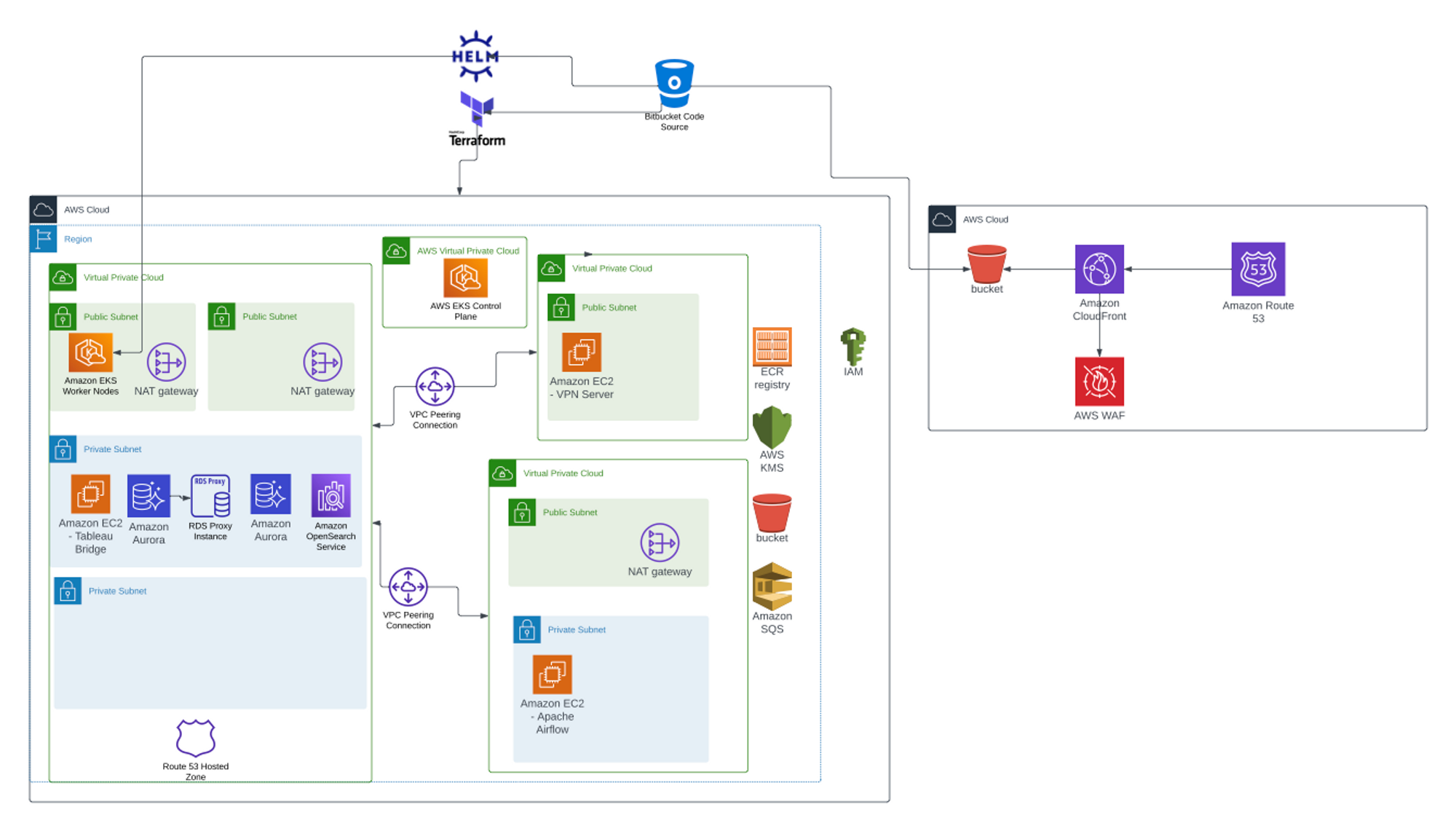
Production environment: Amazon EKS worker nodes with Aurora PostgreSQL, RDS Proxy, OpenSearch Service, and Tableau Bridge in private subnets; VPN server and NAT gateways in public subnets; VPC-peered generic network with Apache Airflow; CloudFront + S3 + Route 53 + AWS WAF for the frontend layer; ECR, KMS, SQS, and IAM as shared services.
Well-Architected audit (CMS Phase 1)
With the foundation in place, Cloudvisor delivered a Well-Architected Review across Security, Cost Optimisation, and Performance Efficiency — producing ~30 prioritised findings, the majority remediated during the engagement.
- Security — Tightened 13 overly-permissive security groups; migrated EKS auth to IAM access entries; moved ECS secrets to AWS Secrets Manager; enforced IMDSv2 fleet-wide; activated GuardDuty, Security Hub, and IAM Access Analyzer; upgraded all ALBs to TLS 1.2/1.3.
- Cost optimisation — Migrated all EBS volumes gp2 → gp3; removed 12 unused volumes (~480 GB); right-sized 18+ EC2 instances; migrated RDS to Graviton; upgraded Aurora off Extended Support; redirected CloudTrail and VPC Flow Logs to S3 + Athena.
- Performance — Added Aurora reader instances and pointed background read traffic at the reader endpoint, distributing load across AZs.
Ongoing Managed Service
Following the audit, Cachet moved onto the full Cloudvisor Managed Service subscription — a continuous engineering partnership rather than a project-by-project engagement.
Bi-weekly environment checks
Automated WAFR-aligned scans against the post-audit baseline, delivered as a structured report with findings remediated by Cloudvisor engineers.
Monthly optimisation cycles
Cost optimisation, architecture drift review, RI/Savings Plan coverage, and time-bound items like certificate expiry and runtime EOL tracking.
24/7 monitoring & alerting
Grafana + CloudWatch alerts across 14+ services, all firing to a dedicated Cachet Slack channel. AWS Config conformance pack runs continuous compliance evaluation in parallel.
Direct engineering access
A dedicated Slack channel for urgent fixes, design questions, and unplanned support — no Statement of Work needed.
CI/CD modernisation
Migrating from Bitbucket Pipelines to GitHub Actions + Argo CD with OIDC-based authentication, build-once/promote-many, and blue/green rollback.
Active roadmap
Phased audit remediation, ongoing FinOps sweeps, and monitoring expansion as new workloads land on EKS.
Results
What started as an infrastructure visibility problem became the foundation for a deeply integrated, continuously improving AWS partnership. Today, Cachet’s platform runs on an environment that is monitored around the clock, audited on a recurring cadence, and backed by a dedicated engineering team — so their internal team can focus entirely on serving gig-economy customers.
- Security posture transformedGuardDuty, Security Hub, IMDSv2, and TLS 1.2/1.3 activated fleet-wide.
- Ongoing improvementBi-weekly and monthly CMS cycles catching regressions before they reach production.
- Deletion protection across the boardEKS, ALBs, NLBs, RDS, and Aurora all protected against accidental deletion.
- 24/7 monitoring across 14+ servicesReal-time Grafana + CloudWatch alerts firing to a dedicated Slack channel.
- Databases encrypted at restMetabase RDS encrypted; Aurora clusters consolidated and upgraded off Extended Support.
- Continuous complianceAWS Config conformance pack continuously evaluated against AWS-recommended controls.
- ~30 audit findings closedAcross Security, Cost Optimisation, and Performance Efficiency.
- Recurring cost savingsGraviton migration, right-sizing, and unused-resource cleanup across compute and storage.











